Navigating Global Privacy Laws: GDPR, CCPA, and Beyond
Sarah Mitchell
9 March 2026
Navigating Global Privacy Laws: GDPR, CCPA, and Beyond
Introduction
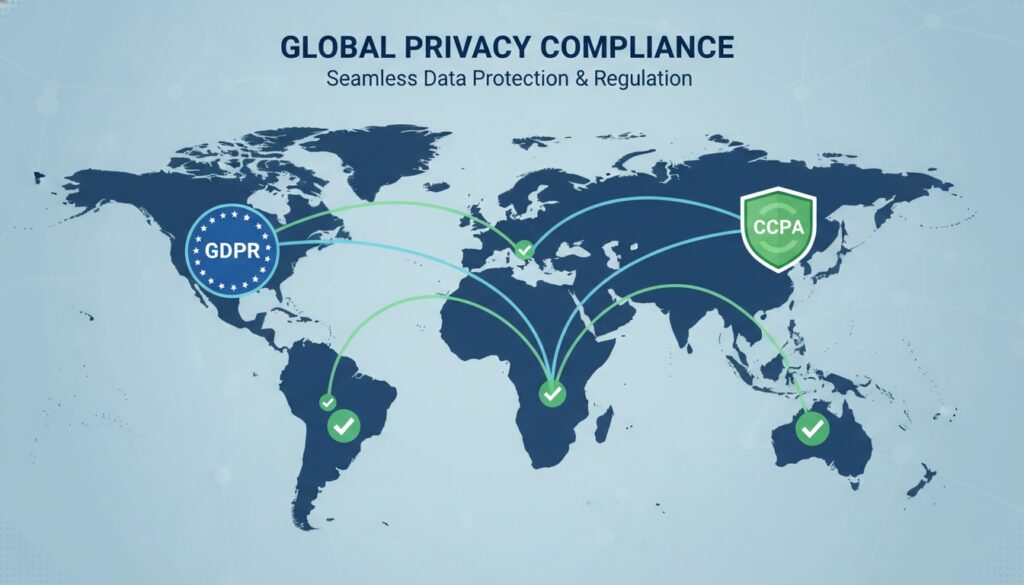
In today’s interconnected digital landscape, data privacy has become the cornerstone of consumer trust and regulatory compliance. With over 5 billion people online globally, businesses are collecting, processing, and storing unprecedented amounts of personal data. This digital revolution has prompted governments worldwide to enact comprehensive privacy legislation, fundamentally reshaping how organizations handle personal information.
From the European Union’s groundbreaking General Data Protection Regulation (GDPR) to California’s Consumer Privacy Act (CCPA), privacy laws are no longer optional considerations—they’re mandatory business imperatives. Companies that fail to comply face devastating financial penalties, reputational damage, and potential operational shutdowns.
The stakes have never been higher. Organizations processing personal data must navigate an increasingly complex web of international privacy regulations, each with unique requirements, enforcement mechanisms, and territorial reach. This comprehensive guide will equip you with the knowledge and strategies needed to achieve compliance across multiple jurisdictions while building consumer trust through transparent data practices.
Understanding GDPR: The Global Privacy Game-Changer
The General Data Protection Regulation (GDPR) revolutionized global privacy standards when it took effect on May 25, 2018. This comprehensive framework doesn’t just apply to European businesses—any organization processing EU residents’ personal data falls under its jurisdiction, regardless of where the company is located.
Core GDPR Principles
GDPR establishes seven fundamental data protection principles that govern all processing activities:
- Lawfulness, fairness, and transparency: Processing must have a legal basis and be conducted transparently
- Purpose limitation: Data collection must serve specific, explicit, and legitimate purposes
- Data minimization: Only collect data that’s necessary for stated purposes
- Accuracy: Maintain accurate and up-to-date personal data
- Storage limitation: Retain data only as long as necessary
- Integrity and confidentiality: Implement appropriate security measures
- Accountability: Demonstrate compliance through documentation and governance
- Right to information: Clear disclosure about data processing
- Right of access: Individuals can request copies of their data
- Right to rectification: Correction of inaccurate information
- Right to erasure: “Right to be forgotten” in certain circumstances
- Right to restrict processing: Temporary halt of data processing
- Right to data portability: Transfer data between service providers
- Right to object: Opt-out of certain processing activities
- Rights related to automated decision-making: Protection against solely automated decisions
- Amazon: €746 million for unlawful processing
- WhatsApp: €225 million for transparency violations
- Google: €90 million for insufficient legal basis
- Have annual gross revenues exceeding $25 million
- Buy, sell, or share personal information of 50,000+ California consumers annually
- Derive 50% or more of annual revenue from selling personal information
- Right to know: What personal information is collected, used, shared, or sold
- Right to delete: Request deletion of personal information
- Right to opt-out: Refuse the sale of personal information
- Right to non-discrimination: Equal service regardless of privacy choices
- Broad territorial scope: Applies to any processing of Brazilian residents’ data
- Sensitive data categories: Special protection for biometric, genetic, and health data
- Data Protection Officer requirements: Mandatory for public bodies and high-risk processing
- Penalties: Up to 2% of revenue or R$50 million per violation
- PIPEDA: Federal law governing commercial activities across provinces
- Provincial laws: Quebec’s Law 25 and British Columbia’s PIPA provide additional requirements
- Breach notification: Mandatory reporting for privacy breaches likely to cause harm
- Singapore: Enhanced penalties up to S$1 million and mandatory breach notification
- Australia: Proposed Privacy Act reforms including individual rights and increased penalties
- India: Draft Personal Data Protection Bill emphasizing data localization
- Map all personal data flows within your organization
- Identify high-risk processing activities requiring enhanced protection
- Document legal bases for each processing purpose
- Assess third-party vendor compliance capabilities
- Implement appropriate technical and organizational measures
- Proactive measures: Anticipate privacy risks before they occur
- Default privacy settings: Maximize privacy protection without user action
- Privacy embedded in design: Integrate protection into system architecture
- Full functionality: Maintain business objectives while protecting privacy
- End-to-end security: Secure data throughout its entire lifecycle
- Visibility and transparency: Ensure all stakeholders can verify compliance
- Respect for user privacy: Keep user interests paramount
- Adequacy decisions: EU-approved countries with equivalent protection
- Standard Contractual Clauses (SCCs): EU-approved contract templates
- Binding Corporate Rules (BCRs): Internal company privacy policies
- Certification mechanisms: Third-party verified compliance programs
- Conduct Transfer Impact Assessments (TIAs) for high-risk destinations
- Implement supplementary measures when local laws may undermine protection
- Maintain detailed transfer records for regulatory inquiries
- Regularly review and update transfer mechanisms
- Immediate detection: Implement monitoring systems for early breach identification
- Initial assessment: Determine breach scope, affected individuals, and risk level
- Regulatory notification: Report to supervisory authorities within 72 hours
- Individual notification: Inform affected persons when high risk exists
- Documentation: Maintain detailed incident records for compliance demonstration
- `Consent management systems`: Capture and manage user preferences
- `Data discovery tools`: Identify personal data across systems
- `Rights management platforms`: Automate individual rights requests
- `Breach detection systems`: Monitor for unauthorized access or disclosure
- `Privacy dashboards`: Provide real-time compliance visibility
- Privacy law fundamentals: Core principles and requirements
- Data handling procedures: Proper collection, use, and disposal practices
- Incident recognition: Identifying potential privacy breaches
- Individual rights processes: Responding to consumer requests
- Vendor management: Ensuring third-party compliance
- Interactive online modules with scenario-based learning
- Department-specific workshops addressing unique risks
- Regular refresher sessions covering regulatory updates
- Simulated breach exercises testing response procedures
- Assess vendor privacy and security capabilities
- Negotiate appropriate contractual protections
- Implement ongoing monitoring and audit rights
- Establish clear incident notification procedures
- Maintain vendor compliance documentation
- Algorithmic transparency: Increased scrutiny of automated decision-making
- Biometric data protection: Enhanced safeguards for biological identifiers
- Children’s privacy: Stricter requirements for minors’ data protection
- Cross-border enforcement: Greater international regulatory cooperation
- Sector-specific requirements: Tailored rules for healthcare, finance, and technology
- Reactive: Responding to privacy incidents and regulatory demands
- Managed: Implementing systematic privacy processes and controls
- Defined: Standardizing privacy practices across the organization
- Quantitatively managed: Using metrics to optimize privacy performance
- Optimizing: Continuously improving privacy practices and competitive advantage
- Conduct a privacy audit to identify current gaps and risks
- Develop a comprehensive privacy policy addressing all applicable regulations
- Train your team on privacy principles and procedures
- Implement technical safeguards to protect personal data
- Establish ongoing monitoring to maintain compliance over time
Individual Rights Under GDPR
GDPR grants individuals unprecedented control over their personal data through eight distinct rights:
Critical Compliance Tip: Organizations must respond to individual rights requests within one month, with possible two-month extensions for complex requests. Failure to respond can result in significant penalties.
GDPR Penalties and Enforcement
GDPR’s enforcement mechanism includes administrative fines up to €20 million or 4% of annual global turnover, whichever is higher. Since implementation, regulators have imposed hundreds of millions in penalties, with major cases including:
Decoding the California Consumer Privacy Act (CCPA)
The California Consumer Privacy Act (CCPA), effective January 1, 2020, marked America’s first comprehensive state-level privacy legislation. Unlike GDPR’s broad territorial scope, CCPA specifically targets businesses that collect California residents’ personal information and meet specific thresholds.
CCPA Applicability Criteria
Businesses must comply with CCPA if they:
Consumer Rights Under CCPA
CCPA grants California consumers four fundamental rights:
CCPA vs. GDPR: Key Differences
| Aspect | GDPR | CCPA |
|——–|——|——|
| Territorial Scope | Global (EU residents) | California residents only |
| Legal Basis | Six lawful bases required | No explicit legal basis requirement |
| Consent Standard | Explicit, informed consent | Opt-out model for sales |
| Penalties | Up to 4% global revenue | Up to $7,500 per violation |
| Data Subject Rights | 8 comprehensive rights | 4 core consumer rights |
Emerging Global Privacy Regulations
Privacy legislation is rapidly expanding beyond GDPR and CCPA, creating a complex global compliance landscape that businesses must navigate strategically.
Brazil’s LGPD (Lei Geral de Proteção de Dados)
Brazil’s General Data Protection Law (LGPD) closely mirrors GDPR’s structure while incorporating unique Latin American perspectives on privacy rights. Key features include:
Canada’s PIPEDA and Provincial Laws
Canada operates under a dual privacy framework combining federal and provincial legislation:
Asia-Pacific Privacy Developments
Singapore’s Personal Data Protection Act (PDPA) and Australia’s Privacy Act represent growing Asia-Pacific privacy consciousness:
Strategic Insight: Organizations should adopt a “privacy-first” approach that exceeds minimum compliance requirements, positioning themselves advantageously as new regulations emerge.
Building a Comprehensive Privacy Compliance Strategy
Successful privacy compliance requires a holistic, risk-based approach that integrates legal, technical, and operational considerations across your entire organization.
Step 1: Conduct Privacy Impact Assessments
Privacy Impact Assessments (PIAs) form the foundation of effective compliance by identifying risks before they materialize:
Step 2: Implement Privacy by Design
Privacy by Design embeds data protection into every aspect of system development and business processes:
Step 3: Develop Cross-Border Data Transfer Mechanisms
International data transfers require appropriate safeguards to maintain protection across jurisdictions:
#### GDPR Transfer Mechanisms:
#### Best Practices for Data Transfers:
Step 4: Establish Incident Response Procedures
Rapid breach response can mean the difference between minor regulatory attention and devastating penalties:
#### 72-Hour Breach Notification Timeline:
Compliance Reality Check: Most privacy breaches result from human error rather than sophisticated cyber attacks. Invest heavily in employee training and awareness programs.
Practical Implementation Guidelines
Translating privacy law requirements into operational reality requires systematic implementation across people, processes, and technology.
Technology Solutions for Privacy Compliance
Privacy management platforms can automate many compliance tasks:
Employee Training and Awareness
Your workforce represents both your greatest privacy risk and most valuable compliance asset:
#### Essential Training Components:
#### Training Delivery Methods:
Vendor and Third-Party Management
Third-party relationships extend your compliance obligations beyond organizational boundaries:
#### Due Diligence Requirements:
Future-Proofing Your Privacy Program
The privacy regulatory landscape continues evolving rapidly, requiring adaptive compliance strategies that anticipate future requirements rather than merely responding to current laws.
Emerging Privacy Trends
Several trends will shape future privacy regulations:
Building Organizational Privacy Maturity
Privacy maturity models help organizations progress from basic compliance to privacy leadership:
Strategic Recommendation: Aim for privacy maturity level 4-5 to maintain competitive advantage and regulatory confidence as requirements continue evolving.
Conclusion
Navigating the complex landscape of global privacy laws requires more than mere compliance—it demands a fundamental shift in how organizations think about personal data. From GDPR’s comprehensive individual rights to CCPA’s consumer-focused approach, privacy regulations represent society’s growing expectation that businesses act as responsible data stewards.
The organizations that will thrive in this privacy-centric world are those that view compliance not as a burden, but as a competitive advantage and trust-building opportunity. By implementing robust privacy programs that exceed minimum requirements, companies can differentiate themselves in crowded markets while building lasting customer relationships based on transparency and respect.
Remember: Privacy compliance is not a destination but an ongoing journey. As new regulations emerge and existing laws evolve, your privacy program must adapt accordingly. The investment you make in comprehensive privacy infrastructure today will pay dividends in regulatory confidence, customer trust, and business resilience tomorrow.
Take Action: Start Your Privacy Compliance Journey Today
Don’t wait for a privacy breach or regulatory investigation to prioritize compliance. Begin implementing these strategies immediately: